BTC was spent twice in 2021 - was BSV?
"…at 21:21 UTC, in the 21st year of the 21st century on a network of 21 quadrillion units, there was a magically small exploit of US$21 on the BTC network, and nobody seems to care—at least not yet."
"…at 21:21 UTC, in the 21st year of the 21st century on a network of 21 quadrillion units, there was a magically small exploit of US$21 on the BTC network, and nobody seems to care—at least not yet."
I wrote that line the day after someone’s BTC disappeared from their wallet and was moved into another wallet on the BTC blockchain: a classic double spend by every definition accepted from 2008 until January 21, 2021. On that date, the small blocker censorship board went into overdrive to redefine one of the most important aspects of the Bitcoin protocol to protect their sacred calf: the fiat value of BTC.
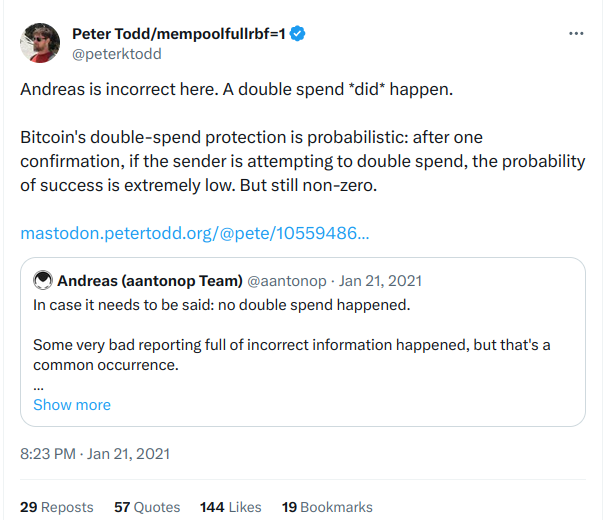
But it really was a double spend! A transaction was included in a block and displayed in the wallet of a BTC user. That balance then disappeared as the block was orphaned and the ledger reorganized by a different node on the network which built the valid block that went forward into history. Recipient A was robbed, and recipient B received his coins instead. To his credit, small blocker Peter Todd swung in to drop a truth bomb.
In 2008, Satoshi Nakamoto explained the way this is designed to work when asked by Hal Finney. He said, “…nodes keep transactions in their working set until they get into a block… The transaction in whichever branch ends up getting ahead becomes the valid one, the other is invalid. If someone tries to double spend like that, one and only one spend will always become valid, the others invalid…”
In the first explanation of a reorganization of the bitcoin ledger (commonly called a “reorg” today), Satoshi explained how an attacker would not be adding new information to the ledger, but actually going back to previously accepted reconciliations and redoing them first while re-writing the history to strike their theft or other vandalism from the accepted history of the longest chain.
“The attacker isn’t adding blocks to the end. He has to go back and redo the block his transaction is in and all the blocks after it, as well as any new blocks the network keeps adding to the end while he’s doing that. He’s rewriting history. Once his branch is longer, it becomes the new valid one.”
The funny thing is that, by the new standards set out by a cacophony of small blockers, BTC’s double spend wasn’t a double spend at all, and the media just let them get away with it. CoinDesk went so far as to say that double spends don’t exist unless they cause inflation, stating “…no bitcoin was ‘double-spent’ because no new coins were added to Bitcoin’s supply,” and then later in the same article stating, “Technically, the same bitcoin was spent twice in this scenario. But one transaction was double-spent to an address on a transaction history that the Bitcoin network does not consider valid.”
In other words, it was a classic double spend!
BTC Core Developer Ben Carman even said, “It’s kinda a double-spend but not really. Normally a double-spend refers to when you intentionally replace a transaction that sends money to someone with one that sends it to your own wallet.”
This is double-speak at its finest!
So why do double spends matter?
Bitcoin is plainly [checks notes] imperfect. It only becomes a problem when malicious actors overpower the honest nodes of the network for extended periods of time, and break the trust model of the system. If users cannot rely on consistent experiences with the network or clear arbitration and remediation of mistakes, then the system is worthless.
Good thing Satoshi thought of this!
In short, the system works because we trust the honest nodes, the reputable peers, the people with whom we have built economic rapport to connect to other reputable peers for the security of the network during times of upheaval and in times of business-as-usual. This is why the proverbial “51% attack” does not exist. If a malicious actor gains majority hash power and uses it to break a bitcoin rule, the minority hash rate of honest nodes on the network becomes the majority by virtue of the fact that they are honest, and they cease acceptance of the blocks of the malicious actor regardless of how much power he brings.
During a war, are the invading barbarians the rightful kings if they win? No. No they are not. Much the same in bitcoin.
Satoshi Nakamoto explains in Section 8 of Bitcoin: A Peer-to-Peer Electronic Cash System: “verification is reliable as long as honest nodes control the network, but is more vulnerable if the network is overpowered by an attacker. While network nodes can verify transactions for themselves, the simplified method can be fooled by an attacker’s fabricated transactions for as long as the attacker can continue to overpower the network. One strategy to protect against this would be to accept alerts from network nodes when they detect an invalid block, prompting the user’s software to download the full block and alerted transactions to confirm the inconsistency.”
In Section 12, Nakamoto clarifies further: “…that quickly becomes computationally impractical for an attacker to change if honest nodes control a majority of CPU power… They vote with their CPU power, expressing their acceptance of valid blocks by working on extending them and rejecting invalid blocks by refusing to work on them. Any needed rules and incentives can be enforced with this consensus mechanism.”
So who wins? The longest chain? Or the honest chain?





